UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE

|
Anthony Y. Fu, PhD Quant analyst, In Algorithmic Trading.
|
Education: 2003, BEng, Computer Science, Tsinghua University, China 2006, PhD, Computer Science, the City University of Hong Kong, Hong Kong SAR, China Curriculum Vita (pdf) |
UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE
Research Interest:
I have great research interest in AI approaches to various computational applications which include Computer Security and Privacy, Web Document Analysis, Information Retrieval, and Natural Language Processing. I am especially interested in devising ideas that can make impact to the digital world. The goal is to release human labors in various areas, and build ideas that can figure out the future of digital lives.
UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE
Publications:
Anthony Y. Fu, Xiaotie Deng, Wenyin Liu, "REGAP: A Tool for Unicode-based Web Identity Fraud Detection", in Journal of Digital Forensics Practice, Publisher: Taylor & Francis, Volume 1, Issue 2, June 2006
Anthony Y. Fu, "Web Identity Security: Advanced Phishing Attacks and Counter Measures", PhD Thesis, Dept. of Computer Science, City University of Hong Kong
Anthony Y. Fu, Liu Wenyin, Xiaotie Deng, "Detecting Phishing Web Pages with Visual Similarity Assessment based on Earth Mover's Distance (EMD) ", in IEEE Transactions on Dependable and Secure Computing, Volume 3(4), pages 301-311, 2006
Anthony Y. Fu, Xiaotie Deng, Liu Wenyin, Greg Little, "The Methodology and an Application to Fight against Unicode Attacks", in Proceedings of SOUPS 2006, Jul, 2006, CMU, Pittsburgh, USA (pdf)
Anthony Y. Fu, Robert C. Miller, Greg Little, and Min Wu "Context Sensitive Password", in Proceedings of SOUPS 2006, Jul, 2006, CMU, Pittsburgh, USA (pdf).
Bessie C. Hu, Anthony Y. Fu, and Xiaotie Deng, "Future Decryption: Secure the Time Sensitive Information", tin Proceedings of SOUPS 2006, Jul, 2006, CMU, Pittsburgh, USA.
Anthony Y. Fu, "Anti-PhAshing", in Security User Studies Workshop of SOUPS 2006, Jul, 2006, CMU, Pittsburgh, USA (pdf, full version)
Anthony Y. Fu, Wan Zhang, Xiaotie Deng, Liu Wenyin, "Safeguard against Unicode Attack: Generation and Application of UC-SimList", in Proceedings of the 15th International World Wide Web Conference, Edinburgh, UK, May, 2006 (pdf)
Anthony Y. Fu, Xiaotie Deng, and Wenyin Liu. "Homograph Attach and Counter Measures". Book section in "Phishing and Counter-measures: Understanding the Increasing Problem of Electronic Identity Theft", publisher: Wiley, pages 81-89, Sep. 2006
Liu Wenyin, Xiaotie Deng, Guanglin Huang, Anthony Y. Fu, "An Anti-Phishing Strategy based on Visual Similarity Assessment", IEEE Internet Computing, Vol. 10, No. 2, pp. 58-65, 2006, also in IEEE Distributed Systems Online, Volume 7 (4), April 2006, (link)
Anthony Y. Fu, Xiaotie Deng, Liu Wenyin, "A Potential IRI based Phishing Strategy ", in the Proceedings of 6th International Conference on Web Information Systems Engineering, Lecture Notes in Computer Science Volume 3806, pages 618 - 619 , WISE 2005, New York, USA, Nov. 20-22, 2005 (pdf, full paper)
Anthony Y. Fu, Liu Wenyin, Xiaotie Deng, "EMD based Visual Similarity for Detection of Phishing Webpages", Proceedings of International Workshop on Web Document Analysis, WDA 2005, Seoul, Korea, Aug. 28, 2005 (pdf)
Anthony Y. Fu, Xiao Wu, Haohuan Fu, "Statistics-based Web Cache Prediction Model", Proceedings of ACM The 6th Postgraduate Research Day 2005, pages 85-93, Poly University of Hong Kong, Mar. 12, 2005 (pdf)
Anthony Y. Fu, Danxia Lin, Gang Liu, "Neural Network Enhanced Sound Source Localization Model for Mobile Terminals", to appear in the 10th Conference on Artificial Intelligence and Applications, TAAI2005, Kaohsiung, Taiwan, Dec. 2-3, 2005 (pdf)
Anthony Y. Fu, Puion Au, "Waiting time prediction: an enhancement for call admission control of mobile system using neural networks", Proceedings of IEEE The 7th International Conference on Advanced Communication Technology, Volume 2, pages 749- 754, ICACT 2005, Phoenix Park, Korea, Feb. 21-23, 2005 (pdf)
Anthony Y. Fu, Haohuan Fu, Pui-on Au, "An Integration Approach of Data Mining with Web Cache Pre-fetching", Lecture Notes in Computer Science Volume 3358, pages 59-63, Publisher: Springer-Verlag, ISPA 2004, Hong Kong, China, Dec. 13-15, 2004 (pdf, link)
UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE
Projects, Systems (sorted by time descendantly):
1. ATVBox is shared online TV selector and player. It contains a lot of online TV channels in its local database. With ATVBox, can search and select your favorite TV programs (news, sports, weather, movies, music, etc.) to watch.
2. ARRA (A Racing Risk Analyst) is shared software which can help analyze the risk and expectation for professional jockeys. It works with Monte Carlo simulation.
3. ASIM (A Smart Information Miner) is shared software to help you retrieve online information (news etc.) and provide active notification when new news arrives. It is very useful tool for making basic analysis in stock markets. If you are a securities/warrants player, you'll find it especially useful.
4. RAP (Reasonable Anti-Phishing) is a commercialized anti-phishing software which can monitor the online dataflow in you network card and report phishing link if found any.
Weblink: http://reasonables.com/antiphishing.aspx
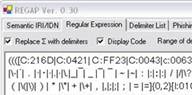
5. REGAP (Regular Expression Generator for Anti-Phishing) is a software which can help you generate complicated and effective regular expression to detect Unicode Attack.
6. CSPass (Context Sensitive Password) is novel design for password protection. The server identity verification is put in to the login process for end users. There are two versions of them (CSPassI and CSPassII).
Weblink: http://antiphishing.cs.cityu.edu.hk/CSPassI
http://antiphishing.cs.cityu.edu.hk/CSPassII
7. IRI/IDN SecuChecker is software which can help you find similar IRI/IDNs in the domain name database. It is based on UC-SimList and three string similarity or patter matching algorithms
Weblink: http://www.mit.edu/~ayf/my_free_sw/IRISecuChecker
8. WWSSList (Word-Word Semantic Similarity List) is database copyrighted by Antiphishing group of City University. With it, we can calculate/measure the semantic similarity or relationships.
E.g. The following words similarity are from WWSSList.
Word1
Word2
Similarity
Left
Right
9.94
Coin
Money
8.56
Student
Coin
0
9. UC-SimList (Unicode Character Similarity List) is database copyrighted by Antiphishing group of City University. With it, we can calculate/measure the visual/semantic similarity of characters in Unicode.
Weblink: http://www.mit.edu/~ayf/IRI
E.g. the follows are the 100% similar characters to "a" in Unicode according to UC-SimList
+U-FF41:a +U-0061:a +U-0430:а
+U-0391:Α +U-FF21:A +U-0410:А +U-0041:A
10. DistAca (Distinguisher for Academia) is software that can help you prove you have done some research/art work/publication for the first time in the word. When you submit your files' encrypted signature to the system, the "distinguishing" process is done. You don't have to disclose your work to the DistAca.
Weblink: http://www.mit.edu/~ayf/my_free_sw/DistAcaDemo.zip
11. ASMS (Anti-Spam Mail Server) is a mail server version of verification image challenge based anti-spam system
Weblink: http://www.cs.cityu.edu.hk/~anthony/my_free_sw
12. ASAO (Anti-Spammer Addin for Outlook 2003) is shared addin for MS Outlook 2003, which can protect you from spam attacks.
Weblink: http://www.mit.edu/~ayf/my_free_sw
The emails that are from unknown addresses (not in the contact list) will be saved in a "Holding box" in Outlook, and challenge emails containing 3d character verification image (as follows) are replied to the senders to recognize.
Others (Projects in Progress, Proposals, and Demos, etc.):
Alive Suspicious Phishing Domain Name Miner (In progress)
BOC Phishing Detection System (In progress)
ActiveX Attack, Demo
Quadratic Splines's Statistical Similarity Approximation (for Unicode Glyphs) Proposal
Anti-Phishing Mail Server (Prototype), volunteers can send suspected phishing emails to report@antiphishing.cs.cityu.edu.hk (our Anti-Phishing Mail Server) to test.
Anti Spamming Mail Server(ASMS)0.61,(Introduction, Download). Based on this idea: Non-ML Anti-Spamming: A Role Based Solution, Research Report of City University of Hong Kong, Dec., 2004, (pdf version)
3D Label Generator 0.2,(Introduction, Download) Example (including 10,000 3DPics), Example Solution
n-Gram Document Similarity Comparer 0.3,(For document similarity ranking, plagiary detection, etc, Download)
ScrachWiKi for Academia, Proposal
UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE
Professional experience:
2008, Quant Analyst, Vegasoul Capital Management, Hong Kong SAR
2007, Research Fellow, Department of Computer Science, City University of Hong Kong, Hong Kong SAR.
2006, Visiting Researcher, Computer Science and Artificial Intelligence Laboratory, Massachusetts Institute of Technology, MA, USA
2003-2006 Teaching Assistant, Department of Computer Science, City University of Hong Kong, Hong Kong SAR.
2005-2006 Semester A CS5286 Algorithms & Techniques for Web Searching
2004-2005 Semester B Distributed System
2004-2005 Semester A Algorithms & Techniques for Web Searching
2003-2004 Semester B Data Base and Programming
2003-2004 Semester A Java Language and Programming
2002~2003, Software Engineer, Gogaku Tech. Co., Tokyo, Japan
UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE
UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE=STATEMACHINE=MODEL=THEORY=UNIVERSE