Mengjia Yan
The Stata Center, 32G-840
32 Vassar St, Cambridge, MA 02139
mengjiay [at] mit [dot] edu
I’m an assistant professor at MIT's
Electrical Engineering and Computer Science Department
and a member of the Computer Science and Artificial Intelligence Laboratory.
My research interest lies in the areas of
computer architecture and security,
with a focus on side channel attacks and defenses.
My group works on exploiting new micro-architectural vulnerabilities and designing comprehensive and efficient defense mechanisms.
Before joining MIT, I earned a Ph.D. degree in Computer Science
from University of Illinois at Urbana-Champaign (UIUC),
where I worked with Professor Josep Torrellas.
I received a B.S. degree in Computer Science
from Zhejiang University, China.
- PhD: If you are a current MIT student, feel free to email me to schedule a meeting. For others, I would like to suggest following the normal PhD application process and indicate me as a preferred reader when submitting your application.
- MEng and UROP: If you are a current MIT student, I would recommend taking 6.5950/6.5951 Secure Hardware Design (was 6.888, 6.S983) or 6.5900 Computer System Architecture (was 6.823). I usually take on students from these courses. If you could not take these courses, I would suggest filling in this form to help me understand your background. For students interested in summer internship positions, please send me an email with your CV and a statement to describe your past project highlights.
News
- 11/2023: We launched the official course website for 6.595 Secure Hardware Design: https://shd.mit.edu. Check out the team and all the exciting materials that we developped in the past three years.
- 10/2023: Will presented EntryBleed at HASP and won the Best Paper Award.
- 10/2023: We decided that our group name will be MATCHA: microarchitecture attacks and challenges.
- 09/2023: SecureLoop is accepted at MICRO'23. EntryBleed is accepted at HASP'23. Congratulations to Kyungmi and Will.
-
06/2023: I am co-organizing two workshops at ISCA'23 (FCRC).
Feel free to check them out.
- PLARCH (Programming Languages for Architecture) is a workshop that brings together researchers working on overlaping topics between PLDI and ISCA.
- MAD (Microarchitectural Attacks and Defenses) Tutorial brings together researchers from industry and academia that want to learn about the state-of-the-art in both microarchitectural attack and defense research.
- 05/2023: My group received the Google Research Scholar Award. Peter and Vincent led the proposal.
- 03/2023: Two papers, Pensieve and Metior, are accepted at ISCA 2023. Congratulations to Yuheng and Peter.
- 01/2023: Two papers, PACMAN and Bigger Fish, are selected as Micro Top Picks from the Computer Architecture Conferences.
- 11/2022: CaSA is selected as an honorable mention in the Top Picks in Hardware and Embedded Security.
- 09/2022: I received the Intel Rising Star Faculty Award, which recognizes research efforts of leading early-career professionals. Link
- 09/2022: I gave a keynote at the SEED workshop (IEEE International Symposium on Secure and Private Execution Environment Design): Looking Beyond Microarchitectural-Only Side Channels. slides splitted slides video
- 07/2022: We are releasing five hands-on lab assignements for studying micro-architectural attacks, including side channels, Rowhammer attacks, and ML-assisted attacks. Feel free to read this SigARCH blog post for more details.
- 06/2022: I am co-organizing the Microarchitectural Attacks and Defenses (MAD) Tutorial (co-located with ISCA'22). Welcome to attend.
- 06/2022: PACMAN got a lot of media coverage. Recommend the article from IEEE Spectrum. PACMAN will also be presetned at DEFCON.
- 06/2022: Bigger Fish was spotlighted at the MIT homepage. Check out the MIT News report.
- 05/2022: A paper on Mesh NoC side channel attacks is accepted at USENIX Security 2022.
- 04/2022: I gave a talk "Security Analysis of Misunderstood Side-channel Attacks and Defenses" at the New England Hardware Security Workshop (NEHSW'22). Workshop Link Video
- 03/2022: Two papers are accepted at ISCA 2022.
- 02/2022: I am co-organizing the Fourth Young Architect Workshop (YArch) in conjunction with ASPLOS 2022.
- 11/2021: DAGguise is accepted at ASPLOS 2022.
- 04/2021: CaSA is selected as a finalist (out of 4) of Intel Hardware Security Academic Award.
- 03/2021: I am co-organizing the Third Young Architect Workshop (YArch) in conjunction with ASPLOS 2021. Please find the schedule of the workshop here.
- 02/2021: Received the NSF Faculty Early Career Development Program (CAREER) Award.
- 07/2020: CaSA and InvarSpec are accepted at MICRO 2020.
- 07/2020: STT is selected as a CACM Research Highlight.
- 06/2020: My PhD thesis "Cache-based Side Channels: Modern Attacks and Defenses" is selected as an honorable mention of the 2020 ACM SIGARCH/IEEE CS TCCA Outstanding Dissertation Award.
- 05/2020: STT is nominated by SIGMICRO as a CACM Research Highlight.
- 01/2020: STT and Microscope are selected as MICRO Top Picks 2020.
- 10/2019: My PhD thesis "Cache-based Side Channels: Modern Attacks and Defenses" is selected for the David J. Kuck Outstanding PhD Thesis Award.
- 10/2019: "Speculative Taint Tracking (STT): A Comprehensive Protection for Transiently Accessed Secrets" won the best paper award at MICRO 2019.
- 09/2019: "Cache Telepathy" is accepted at USENIX Security 2020.
>> older news...
Students
- Peter Deutsch
- Yuheng Yang (EECS MathWorks Fellowship, MIT EECS Master Thesis Award)
- Joseph Ravichandran (NSF Fellowship, Draper Scholar, Department Outstanding TA Award, MIT EECS Master Thesis Award)
- Shixin Song (Ho-Ching and Han-Ching Fund Award)
- Daniël Trujillo (NDSEG Fellowship)
- Tingzhen (Roger) Dong
- Vincent Ulitzsch (TU Berlin)
- Kunpeng Wang (Shanghai Jiaotong University)
- William Liu (Robert M. Fano UROP Award, Department Outstanding TA Award)
- Kelly Xu
- Jonah Romero
- Kosi Nwabueze
- David Choi
- PostDoc
- Mengyuan Li (PostDoc'22-24 → Assistant Professor, USC)
- UROP/MEng
- Shih-Yu (Leo) Wang (MEng'25)
- Natalie Muradyan (MEng'24 → D. E. Shaw)
- Muhammad Abdullah (BS'24 → Siemens EDA)
- Shashvat Srivastava (MEng'23 → Voleon)
- Miguel Gomez-Garcia (Co-advised with Srini Devadas, MEng'23 → Multiply Labs)
- Georgia E Shay (MEng'23 → AMD)
- Jay Lang (BS'22 → Apple)
- Jack Cook (Robert M. Fano UROP Award, Rhodes Scholar, NSF Fellowship, BS'22 → University of Oxford)
- Brandon John (MEng'22 → Lincoln Lab)
- Miles Dai (Harold Hazen Teaching Award, MEng'21 → Google OpenTitan)
- Visiting Undergrads
- David Langus Rodriguez (MIT Lincoln Lab → Cornell PhD)
- Alec Petridis (UCSB)
- Tingzhen (Roger) Dong (BS'24 SUSTech → MIT PhD)
- Yi Chen (BS'23 Zhejiang University → University of Michigan PhD)
- Boru Chen (BS'22 Zhejiang University → UIUC PhD)
- Yuheng Yang (BS'21 University of Chinese Academy of Sciences → MIT PhD)
Teaching
- 6.1910[6.004] Computation Structures:
Spring 2021 (Recitation), Fall 2021
- 6.5900[6.823] Computer System Architecture:
Spring 2020, Fall 2022, Fall 2023
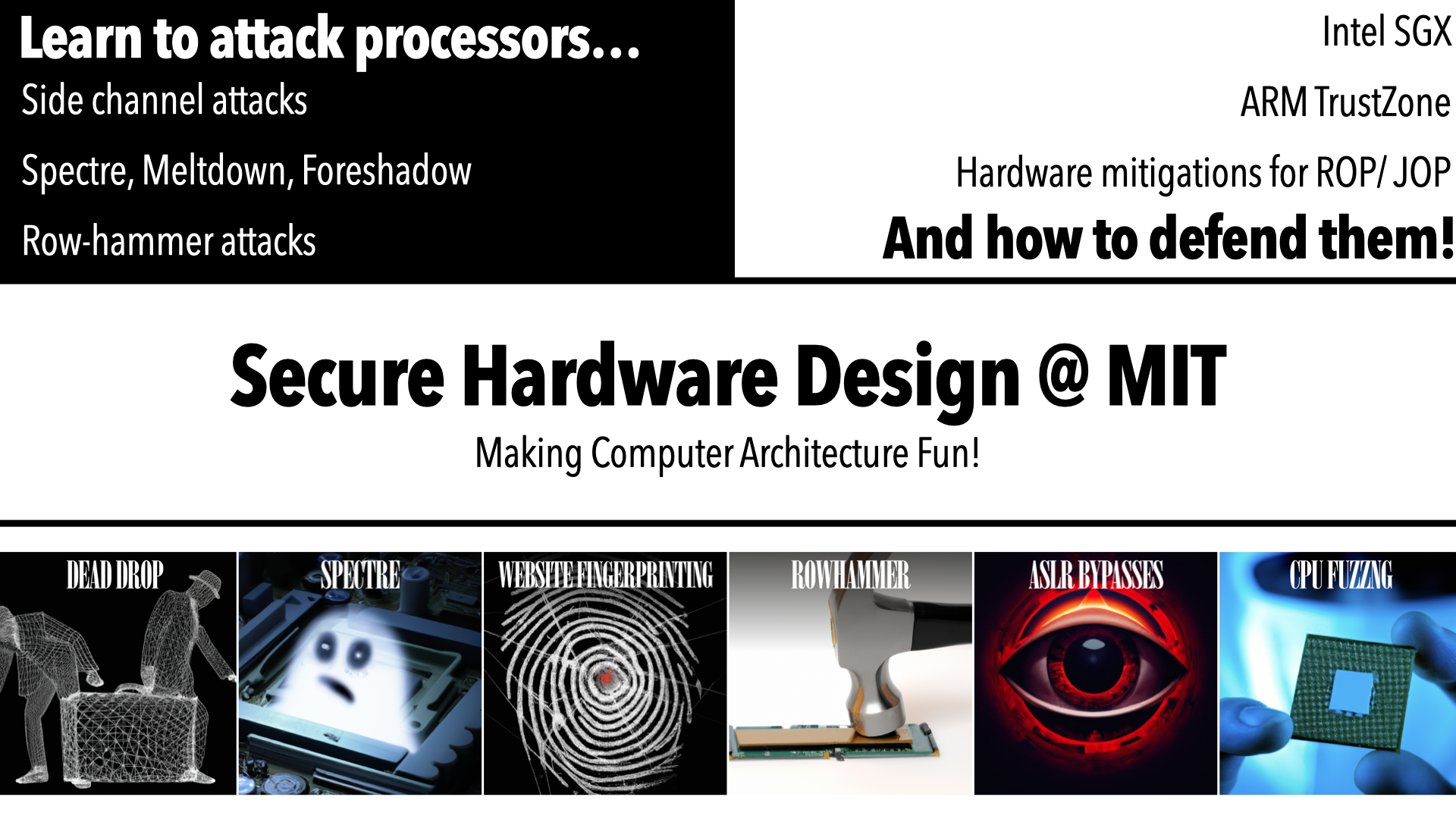
- 6.5950/6.5951[6.888,
6.S983] Secure Hardware Design:
Fall 2020, Spring 2022, Spring 2023, Spring 2024
Publications
- RTL Verification for Secure Speculation Using
Contract Shadow Logic;
Qinhan Tan*, Yuheng Yang*, Thomas Bourgeat, Sharad Malik,
Mengjia Yan;
ASPLOS, 2025.
paper slides code - Oreo: Protecting ASLR Against Microarchitectural Attacks;
Shixin Song, Joseph Zhang, Mengjia Yan;
NDSS, 2025.
paper (extended version) - DelayAVF: Calculating Architectural Vulnerability Factors
for Delay Faults;
Peter Deutsch*, Vincent Ulitzsch*, Sudhanva Gurumurthi, Vilas
Sridharan, Joel Emer,
Mengjia Yan;
MICRO, 2024.
IEEE Micro's Top Picks Honorable Mention
paper slides code - SecureLoop: Design Space Exploration of Secure DNN Accelerators;
Kyungmi Lee, Mengjia Yan, Joel S Emer, Anantha Chandrakasan;
MICRO, 2023.
paper slides code MIT News - EntryBleed: A Universal KASLR Bypass against KPTI on Linux;
William Liu, Joseph Ravichandran, Mengjia Yan;
HASP (with MICRO), 2023.
HASP Best Paper Award
paper slides blog post - Pensieve: Microarchitectural Modeling for Security Evaluation;
Yuheng Yang, Thomas Bourgeat, Stella Lau, Mengjia Yan;
ISCA, 2023.
paper slides code ISCA Lightning Talk - Metior: A Comprehensive Model to Evaluate Obfuscating Side-Channel Defense Schemes;
Peter W. Deutsch, Weon Taek Na, Thomas Bourgeat, Joel Emer, Mengjia Yan;
ISCA, 2023.
paper slides code ISCA Lightning Talk MIT News - PACMAN: Attacking ARM Pointer Authentication with Speculative Execution;
Joseph Ravichandran*, Weon Taek Na*, Jay Lang, Mengjia Yan;
ISCA, 2022.
IEEE Micro's Top Picks IEEE Micro article
paper slides video (ISCA Talk) DEFCON talk
pacmanattack.com ARM Security Article
PACMAN 2.0: code (including Rust PoC, PacmanKit, PacmanPatcher)
Media Coverage: [IEEE Spectrum] [TechCrunch] [MIT News] [The Register] [Dark Reading] [机器之心] [Macworld] [Cryotweaks] [Tom's Hardware] [New York Daily Paper] [VentureBeat] [phoronix] [channel969] [9To5Mac] [CHAROPF] [The Hacker News] [Security Affairs] - There's Always a Bigger Fish: A Clarifying Analysis of a Machine-Learning-Assisted Side-Channel Attack;
Jack Cook, Jules Drean, Jonathan Behrens, Mengjia Yan;
ISCA, 2022.
IEEE Micro's Top Picks IEEE Micro article
Intel Hardware Security Academic Award 2024 First Place Winner
paper slides video (polished version) open-source release demo MIT News - Don’t Mesh Around: Side-Channel Attacks and Mitigations on Mesh Interconnects;
Miles Dai*, Riccardo Paccagnella*, Miguel Gomez-Garcia, John McCalpin, Mengjia Yan;
USENIX Security, 2022.
paper slides video open-source release MIT News - DAGguise: Mitigating Memory Timing Side Channels;
Peter W. Deutsch*, Yuheng Yang*, Thomas Bourgeat, Jules Drean, Joel Emer, Mengjia Yan;
ASPLOS, 2022.
paper slides video open-source release MIT News NSF Research News - SpecTaint: Speculative Taint Analysis for Discovering Spectre Gadgets;
Zhenxiao Qi, Qian Feng, Yueqiang Cheng, Mengjia Yan, Peng Li, Heng Yin, Tao Wei;
NDSS, 2021.
paper - CaSA: End-to-end Quantitative Security Analysis of Randomly Mapped Caches;
Thomas Bourgeat*, Jules Drean*, Yuheng Yang, Lillian Tsai, Joel Emer, Mengjia Yan;
MICRO, 2020.
Intel Hardware Security Academic Award 2022 Finalist
Top Picks in Hardware and Embedded Security Honorable Mention
paper slides talk video - Speculation Invariance (InvarSpec): Faster Safe Execution Through Program Analysis;
Zirui Zhao, Houxiang Ji, Mengjia Yan, Jiyong Yu, Christopher W. Fletcher, Adam Morrison, Darko Marinov, Josep Torrellas;
MICRO, 2020.
paper slides - Cache Telepathy: Leveraging Shared Resource Attacks to Learn DNN Architectures;
Mengjia Yan, Christopher W. Fletcher, Josep Torrellas;
USENIX Security, 2020.
paper - Speculative Taint Tracking (STT): A Comprehensive Protection for Speculatively Accessed Data;
Jiyong Yu, Mengjia Yan, Artem Khyzha, Adam Morrison, Josep Torrellas, Christopher W. Fletcher;
MICRO, 2019.
Best Paper Award
IEEE Micro's Top Picks
Communications of the ACM Research Highlight (CACM)
paper formal analysis/security proof
- SecDir: A Secure Directory to Defeat Directory Side-Channel Attacks;
Mengjia Yan, Jen-Yang Wen, Christopher Fletcher, Josep Torrellas;
ISCA, 2019.
paper slides - MicroScope: Enabling Microarchitectural Replay Attacks;
Dimitrios Skarlatos, Mengjia Yan, Bhargava Gopireddy, Read Sprabery, Josep Torrellas, Christopher Fletcher;
ISCA, 2019.
IEEE Micro's Top Picks
paper slides open-source release - Attack Directories, Not Caches: Side Channel Attacks in a Non-Inclusive World;
Mengjia Yan, Read Sprabery, Bhargava Gopireddy, Christopher W. Fletcher, Roy Campbell, Josep Torrellas;
S&P, 2019.
paper slides talk video - InvisiSpec: Making Speculative Execution Invisible in the Cache Hierarchy;
Mengjia Yan, Jiho Choi, Dimitrios Skarlatos, Adam Morrison, Christopher W. Fletcher, Josep Torrellas;
MICRO, 2018.
IEEE Micro's Top Picks Honorable Mention
paper slides open-source release
- UCNN: Exploiting Computational Reuse in Deep Neural Networks via Weight Repetition;
Kartik Hegde, Jiyong Yu, Rohit Agrawal, Mengjia Yan, Michael Pellauer, Christopher W. Fletcher;
ISCA, 2018.
paper - Record-Replay Architecture as a General Security Framework;
Yasser Shalabi, Mengjia Yan, Nima Honarmand, Ruby B Lee, Josep Torrellas;
HPCA, 2018.
paper - Secure Hierarchy-Aware Cache Replacement Policy (SHARP): Defending Against Cache-Based Side Channel Attacks;
Mengjia Yan, Bhargava Gopireddy, Thomas Shull, Josep Torrellas;
ISCA, 2017.
paper slides - ReplayConfusion: Detecting Cache-based Covert Channel Attacks Using Record and Replay;
Mengjia Yan, Yasser Shalabi, Josep Torrellas;
MICRO, 2016.
paper slides
- Cache-based Side Channels: Modern Attacks and Defenses;
Mengjia Yan; Ph.D. Thesis, 2019.
2020 ACM SIGARCH/IEEE CS TCCA Outstanding Dissertation Award Honorable Mention
UIUC David J. Kuck Outstanding PhD Thesis Award
thesis
Service
- 2025: ASPLOS, CCS (Hardware Security Track Co-chair)
- 2024: ASPLOS, ISCA, Top Picks in Hardware and Embedded Security (TPC Co-chair)
- 2023: ISCA, Oakland, Micro Top Picks
- 2022: ISCA, MICRO, ASPLOS, HPCA
- 2021: ISCA (ERC), MICRO, ASPLOS, HPCA, Micro Top Picks
- 2020: ISCA, MICRO, ASPLOS (ERC)
- 2019: MICRO
- Workshop on Programming Languages for Architecture (PLARCH) 2023 (with ISCA and PLDI)
- Tutorial on Microarchitectural Attacks and Defenses (MAD) with ISCA
- Young Architect Workshop (YArch) with ASPLOS
- EECS Rising Stars Workshop 2021
- New England Hardware Security Day (NEHWS)
- Publicity Co-chair for ISCA 2023
- Publicity Co-chair for ASPLOS 2023
- Area Vice-chair for the Computer Architecture area in IPDPS 2021
- Publication Chair for MICRO 2021
- Registration Chair for ISPASS 2020